Android 17 is Getting a Post Quantum Cryptography Upgrade

Following their shortening of the deadline to implement post-quantum encryption to 2029, Google today announced the “first phase” of its post-quantum transition.
Google is upgrading Android with a quantum-resistant chain of trust, starting from Android Verified Boot all the way up to app signing.
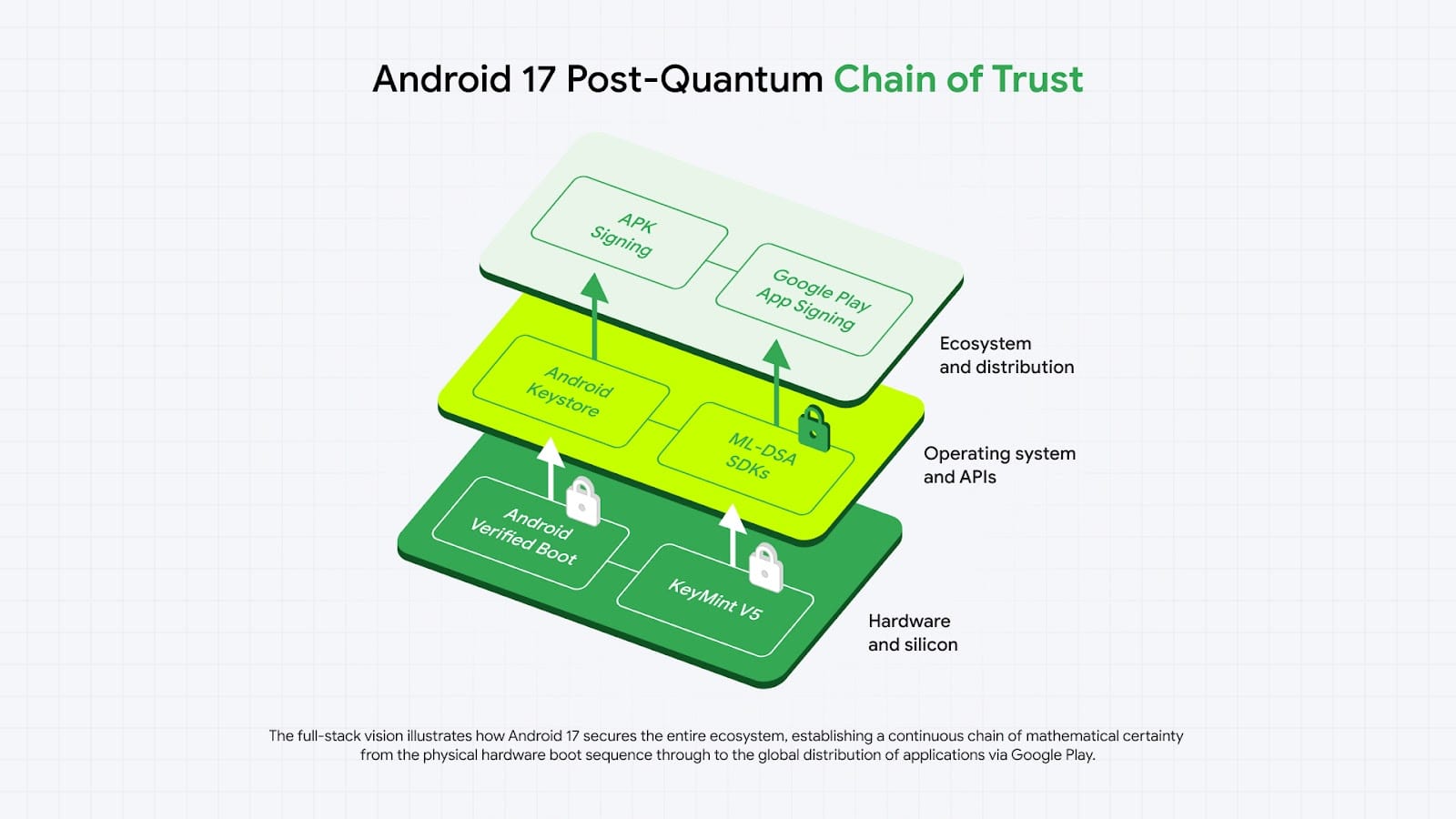
The chains of trust is what allows your operating system to verify you’re running trusted software. You start with a hardware root of trust laid down in the factory which can’t be changed. Then the hardware root of trust verifies the next component, which verifies the next component and so on.
Android 17 will support the recently finalized NIST standard Module-Lattice-Based Digital Signature Algorithm (ML-DSA). This algorithm allows for quantum-safe signatures.
Android Verified Boot is essential for security on your system: after all, if you can’t verify you’re running trusted software, then an attacker could run anything they want.
They’re also migrating remote attestation to PQC.
By updating KeyMint's certificate chains to support quantum-resistant algorithms, devices can securely prove their state to relying parties, maintaining trust in a post-quantum environment.
They're bringing the new cryptography to app signing, too: developers can now utilize the new PQC in the Android Keystore, keeping key material securely isolated from the main operating system. The new ML-DSA-65 and ML-DSA-87 cryptography will be available using the standard KeyPairGenerator API, meaning developers won't need to roll their own crypto.
Implementing lattice-based cryptography, which requires significantly larger key sizes and memory footprints than classical elliptic curve cryptography, within the severely resource-constrained Trusted Execution Environment (TEE), represents a major engineering achievement. This capability is designed to support the hardware roots of trust and can now generate and verify post-quantum signatures.
Cryptographers have long warned that quantum computers could eventually pose a risk to classical cryptography. Quantum computers are always getting better, and recent advances in quantum decryption algorithms have made the prospect seem closer than ever.
While Google now puts that day at just three years away in 2029, the NSA puts the deadline for transitioning to PQC at 2033.
Quantum computers don't just threaten data in the future though: threat actors are collecting encrypted data today in the hopes that it will be possible to decrypt at a later date, a "harvest now, decrypt later" attack.
Messengers like Signal and iMessage have implemented PQC already in preparation for the coming threat. Apple has been adding PQC to their operating system and making it available to developers to use via APIs, and Google have been adding PQC to Chrome and offering it via their cloud services.

Community Discussion