Coruna Malware Targeting iOS Spotted by Google Threat Intelligence

Google Threat Intelligence Group has identified a “powerful exploit kit” targeting iPhones running iOS 13.0 to 17.2.1 used by a surveillance company and crypto-stealing sites.
The kit, dubbed Coruna internally by its developers, contained five full iOS exploit chains and 23 total exploits, some of which were non-public exploits and mitigation bypasses.
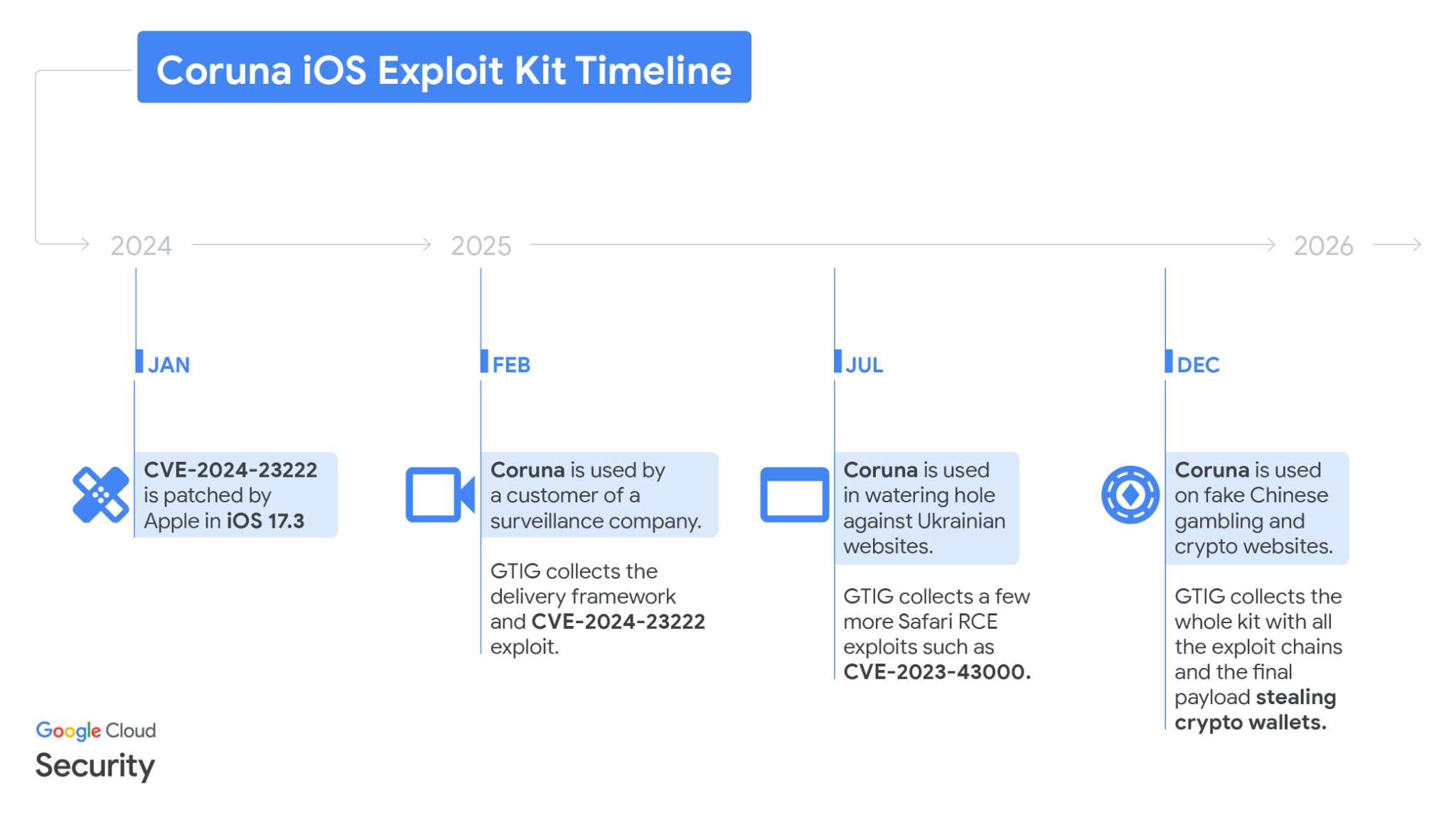
GTIG initially tracked it through its use by a customer of a surveillance vendor, a seller of spyware that’s used against targeted individuals’ devices.
They later were able to obtain the full exploit kit after observing it being used in watering hole attacks (attacks where a website frequently visited by the target is hacked to distribute malware to them) against Ukrainians by UNC6353, a suspected Russian espionage group.
They then found it being used by fake Chinese gambling and crypto websites looking to empty users’ crypto wallets.
The distribution across multiple seemingly unrelated attacks implies an active “second-hand” market for zero-day exploits. Beyond the exploits themselves, attackers can reuse advanced exploitation techniques with new exploits once the old ones are patched.
GTIG says the kit is not effective against the latest version of iOS, so users should update their devices urgently.
The framework first starts and advanced fingerprinting module, collecting data points to determine what specific iPhone model and iOS version the user is running. Then, it loads the appropriate remote code execution (RCE) exploit and then a pointer authentication code (PAC) bypass, a security mitigation to prevent memory corruption.
GTIG describes the kit as “extremely well engineered,” with all the pieces sharing a common framework.
Interestingly, the malware quits if the phone is in Lockdown Mode or Safari is in Private Browsing mode.
The list of 23 exploits covers different ranges of iOS versions and all have their own names such as buffout, bluebird, terrorbird, cassowary, etc. Interestingly, the codenames are all in English.
The founder of iVerify, Rocky Cole, told Wired that he believes the US government might be behind Coruna.
This is the first example we've seen of very likely US government tools – based on what the code is telling us – spinning out of control and being used by both our adversaries and cybercriminal groups.
Boris Larin, principal security researcher at Kaspersky disagrees. He told The Register "we see no evidence of actual code reuse in the published reports to support attributing Coruna to the same authors."
It’s good to know that the exploit used was patched before GTIG were even able to find the exploit kit. It just goes to show how important updating your software is.

Community Discussion