Notepad++’s New Update System is “Robust and Effectively Unexploitable”

Notepad++ has released a blog post describing the security enhancements they’ve made since the state-sponsored hack earlier this month, highlighting their new “double lock” update mechanism.
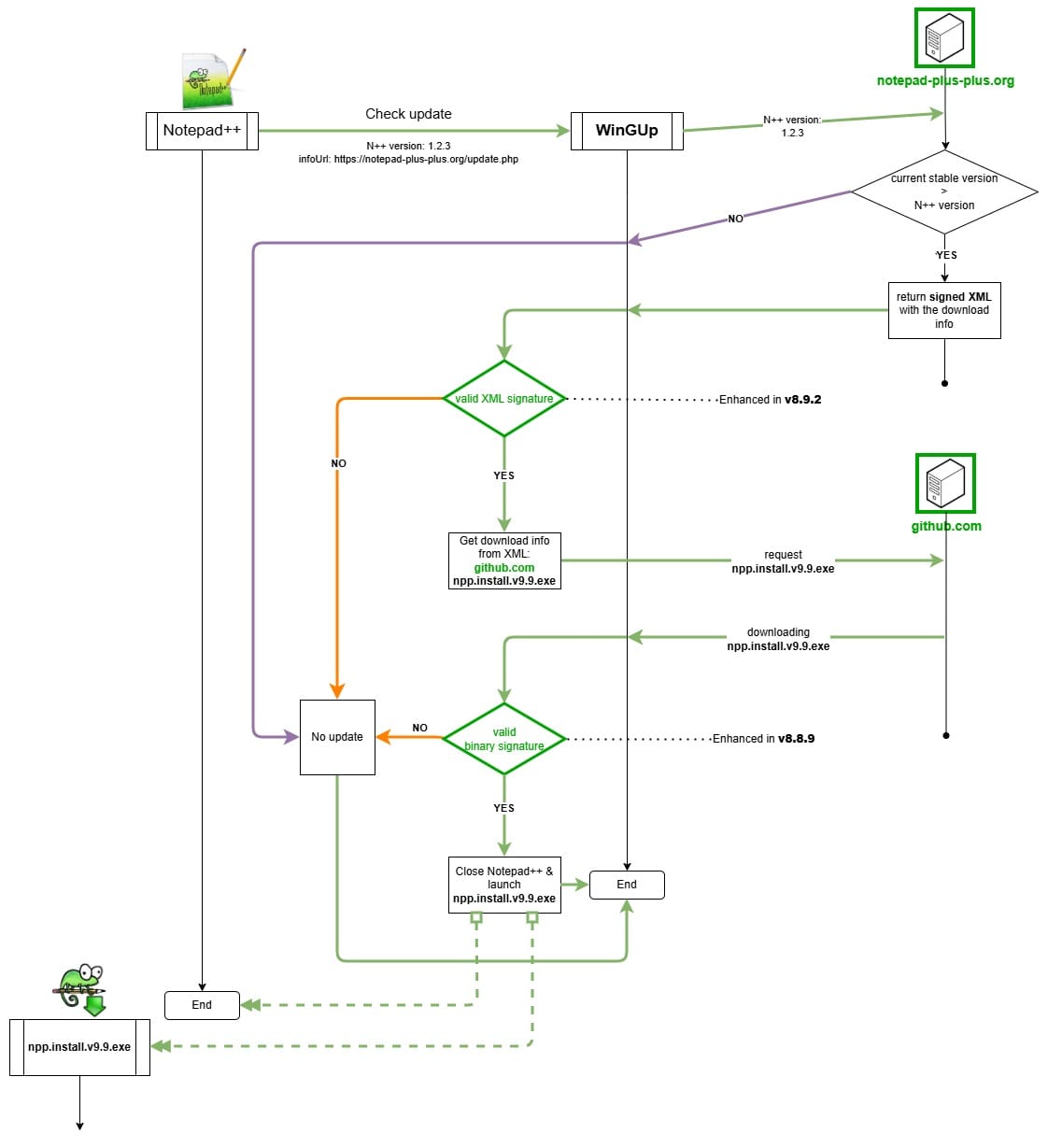
The release marks the finalization of the measures that were promised in the previous announcement. Namely, enforcing the signed XML file returned by the update server.
In their previous post, Notepad++ detailed the improvements they made to improve security.
They switched to a new service provider that has “significantly stronger security practices.”
The WinGup updater that handles automatic updates was updated to verify the certificate and the signature of the downloaded installer that they get from their GitHub.
Additionally, they started signing the XML returned by the update server.
However, they didn’t start enforcing the signature until this update.
This completes what they call the “double lock” design, which makes it “robust and effectively unexploitable.”
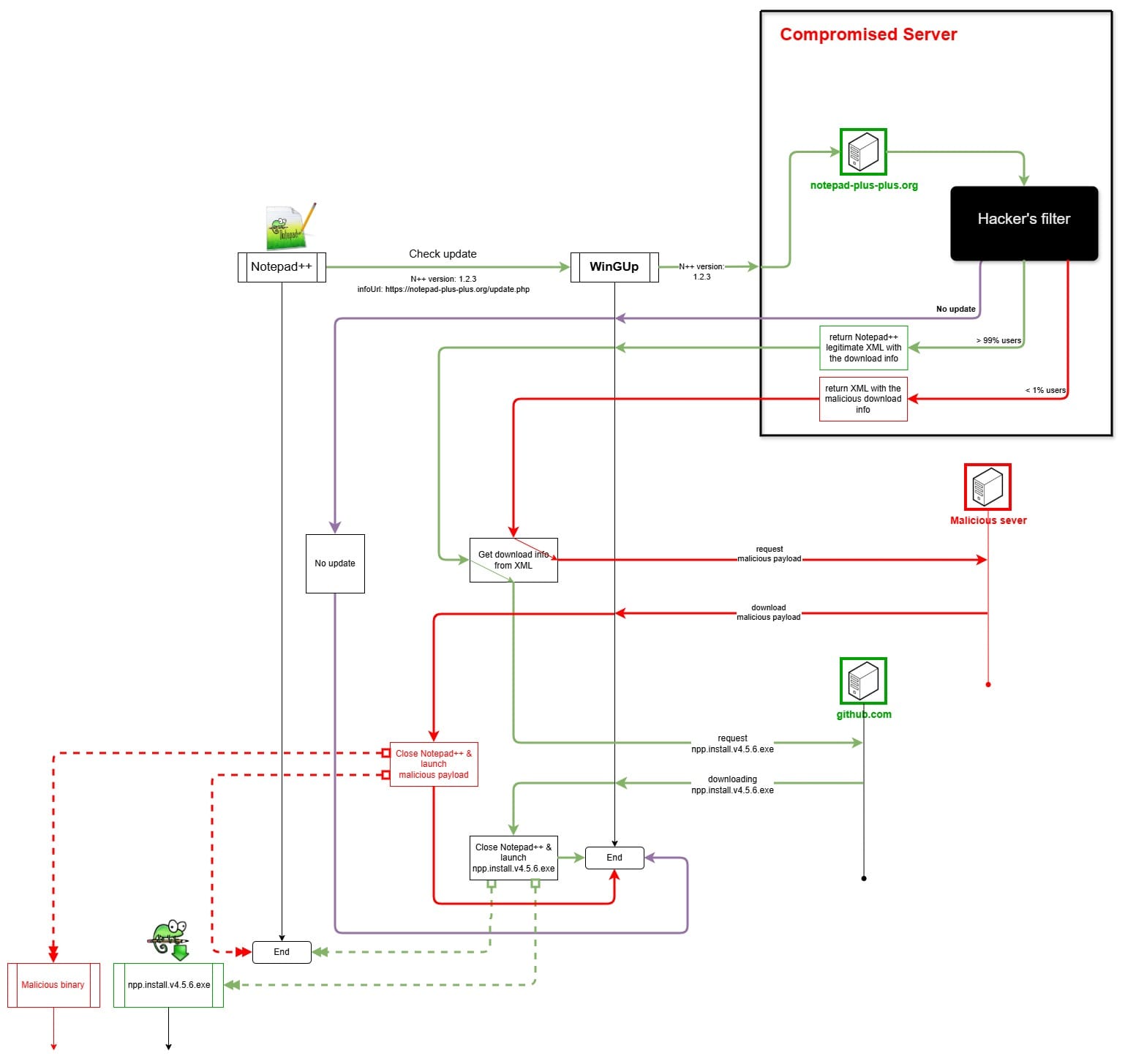
Compare this to their previous architecture that didn’t verify the XML file or the WinGup updater that was hijacked:
Props to Notepad++ for the work they’ve done, but I have to question the claim that the new auto updater is “unexploitable.” It did stop the previous attack, but there’s no guarantee it’ll stop future attacks that target parts of the update process that were missed this time.
They could avoid implementing their own autoupdater altogether and ship their software on the native app store of the operating system, such as the Microsoft Store in Windows, the App Store on macOS, or Flathub on Linux. These stores allow for apps to be signed to verify they’re from the true developers and they provide an update mechanism that they can utilize.
If every piece of software on your system has its own updater, any of which could have similar issues to the Notepad++ updater, then you open yourself up to similar attacks for every single piece of software on your entire system.
Aside from security, it’s pretty annoying when every app on your desktop has its own autoupdater that bugs you individually whenever there’s a new update instead of having them all in one place handled in the background.
A similar attack from years ago happened with CCleaner. Attackers were able to take over the company’s servers, apparently for seven months, five of which were before they even served the malicious program.
The fact that it goes unnoticed for months at a time is concerning. The Notepad++ attack lasted for 7 months as well. Every single program on your machine that you download from the developers’ website or that has its own autoupdater could potentially be vulnerable to these types of supply chain attacks.

Community Discussion